It is Likely Voting Machines Will Be Hacked this November Election
Voters have more to worry about than candidates this election season, as they must also be concerned with hacking at the polls. Leading cyber security experts claim hacking is a distinct possibility, and could impact the outcome of the Presidential race in particular.
Background
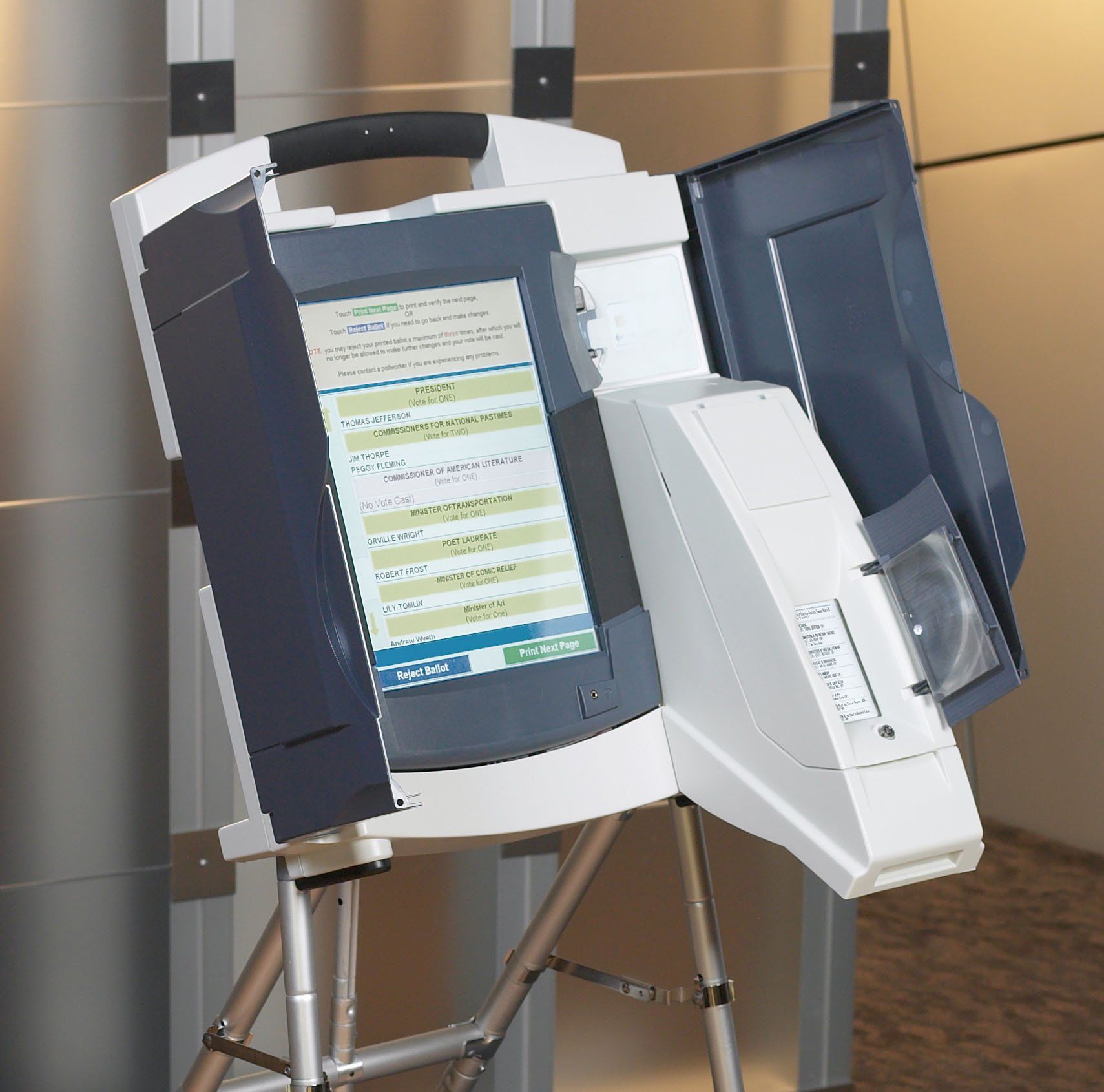
The Help America Vote Act of 2002 was designed to phase out the punch card ballots that resulted in the U.S. Supreme Court deciding the case of Bush vs. Gore. This act resulted in thousands of voting machines across the country being replaced with newer electronic models. The problem with this is that officials did not take into consideration the new challenges electronic voting machines would bring. As such, many of them are currently running Windows XP or an older version of Windows for which a security patch has not been released since April 2014.
Decertified Machines
The fact that voting machines are insecure resulted in Virginia officials decertifying thousands of WinVote machines. The decertification happened after a security team discovered that “anyone within a half-mile could have modified every vote undetected.” The vendor has now gone out of business, meaning there is no way to correct the deficiency aside from replacing the machines. This Virginia case is not an isolated one, as many of the other electronic machines are also subject to hacking. According to Lawrence Norden of the Brennan Center, perfectly secure computers (or computerized voting machines) are an impossibility.
Hacked Databases
Recently, Russian hackers made two separate attempts to hack statewide databases containing voter registration information. These hackers are credited with lifting data from as many as 200,000 voters in Illinois, prompting the FBI to send out a flash alert to agencies nationwide. The flash alert asked officials to be on the lookout for any similar cyber intrusions. According to an unnamed source, there is “serious concern” that the Kremlin may try to interfere in this year’s Presidential election process. The hacks that took place in Illinois are simply more evidence of this.
Challenges with Upgrading
A lack of funding is what prevents most polling locations from upgrading to more reliable, secure machines. As such, only a handful of areas have purchased new equipment in the past year. It seems that many state legislators are unwilling to fund new voting machines unless there is some type of crisis at the polls. Making matters worse is the fact that many states currently do not have an audit system in place. This includes states such as Kentucky and Pennsylvania that require election audits, but do not have any paper trails in place to help them complete one.
More than 75% of all Americans will still vote on paper ballots this fall, yet that does not mean that hacking is not a concern. The remaining 25% will vote on electronic machines, leaving enough leeway for hackers to affect the outcome. The FBI recommends that states contact their Board of Elections to see if unusual activity on their inbound or outbound logs has been detected. Doing so will hopefully ensure that breaches are corrected before voting begins.
The post It is Likely Voting Machines Will Be Hacked this November Election appeared first on SDTEK | San Diego, CA.