What is E-Waste and Where Should You Properly Dispose Of It
As a managed service provider, it’s not only our job to provide high quality IT support for our clients, but to also provide helpful technology tools for the community. In this day in age, many people do rely heavily upon electronics. Working on a brand new computer or using a top of the line printer is fun and exciting, however, over time new technology will grow old and will need to be replaced. As these devices become no longer useable they can fall into a category of electronics called e-waste.
Let’s take a closer look at e-waste and how you should properly dispose of it.
What is E-Waste?
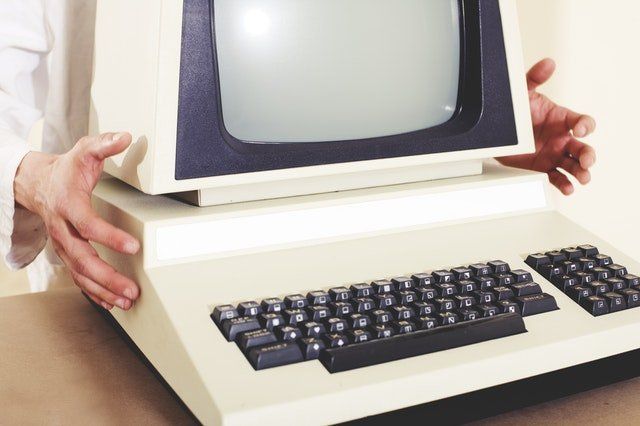
E-waste is basically electronics that are on their last leg, devices that are about to stop working or have completely stopped working all together. Electronics that are no longer functioning are not helpful anymore in the office. But that doesn’t mean the journey for a non-working device stops there. E-waste can typically be recycled, re-used, resold or refurbished into something else.
Examples of E-Waste are as follows:
- Computers
- Printers
- Tablets
- Cell Phones
- Monitors
- Laptops
- Electronics around the home or office
Here are some helpful reasons from an article on https://www.thebalancesmb.com about why it is important to recycle electronics:
- Rich Source of Raw Materials: Internationally, only 10-15 percent of the gold in e-waste is successfully recovered while the rest is lost. Ironically, electronic waste contains deposits of precious metal estimated to be between 40 and 50 times richer than ores mined from the earth, according to the United Nations.
- Solid Waste Management: Because the explosion of growth in the electronics industry, combined with short product life cycle has led to a rapid escalation in the generation of solid waste.
- Toxic Materials: Because old electronic devices contain toxic substances such as lead, mercury, cadmium and chromium, proper processing is essential to ensure that these materials are not released into the environment. They may also contain other heavy metals and potentially toxic chemical flame retardants.
- International Movement of Hazardous Waste: The uncontrolled movement of e-waste to countries where cheap labor and primitive approaches to recycling have resulted in health risks to residents exposed to the release of toxins continues to an issue of concern.
Where Should You Properly Dispose of E-Waste?
First off we want to note, for some communities it is illegal to throw away e-waste in regular garbage and recycling bins. Please always check with your city to find out what their policy is for e-waste and where they recommend to drop it off at.
In order to dispose properly of e-waste, there are specific locations you can visit where you can safely drop off your electronics. There are local recycling centers that can collect your e-waste. When your electronics are donated, they can be repurposed or recycled into something else. Also, something to keep in mind before dropping off a computer, tablet, laptop, etc. you will want to make sure all your personal information has been removed from that device.
Here’s a link to help get you started on where to go to properly dispose of your e-waste: https://www2.calrecycle.ca.gov/electronics/eRecycle/
The safe disposal of electronic devices is important for a community. Please make sure to check out where is the best place in your city to drop off an electronic device that is no longer usable. You’ll be not only helping out your neighbors but the environment too.
The post What is E-Waste and Where Should You Properly Dispose Of It appeared first on SDTEK | San Diego, CA.


